ThreatConnect + Threater: Advanced Threat Intelligence Integration


An Ongoing Blog Series Highlighting Threater’s Best-In-Class Threat Intelligence
Integrating with our Threat Intelligence Platform partners, means helping to bring their mission forward. In the case of ThreatConnect, that means enabling organizations to break-down silos between teams, streamline and align security processes, integrate technologies and measure the impact of their efforts based on risk-reduction. Together, we bring security to work!
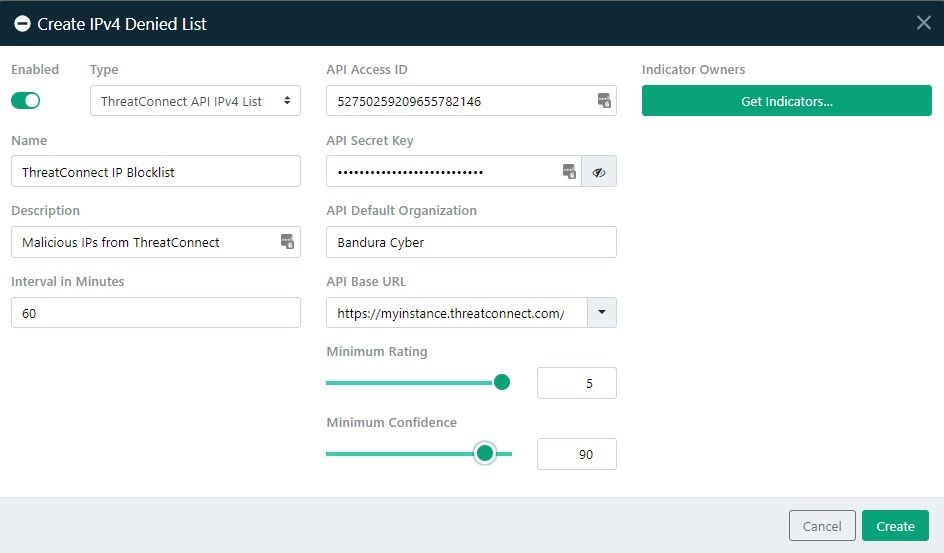
The Threater platform integrates threat intelligence from various sources to block attacks from up to 150M malicious IPs and domains in real-time with no latency. This integration enables mutual customers to easily create IP and domain Denied Lists in Threater based upon the curated, relevant threat intelligence from available within ThreatConnect to actively protect your environment. Threat intelligence is automatically synchronized, ensuring network protection is always current and eliminating manual efforts.
ThreatConnect and Threater together improve security and efficiency while maximizing threat intelligence ROI by integrating and automating the full threat intelligence lifecycle – aggregation, contextualization, and protection.
Check out our datasheet to learn more!
Also watch this video from our very own Jay Brooke to see how easy it is to make threat intelligence from ThreatConnect actionable in the Threater platform using the “out-of-the-box” ThreatConnect plugin.
As always:
If you are a current customer and have any questions, feel free to reach out to our customer support team at support@threater.com
If you’d like to learn more about Threater’s platform integrations, visit the Integrations tab on www.threater.com If you’d like to get started with Threater’s platform today, contact sales@threater.com