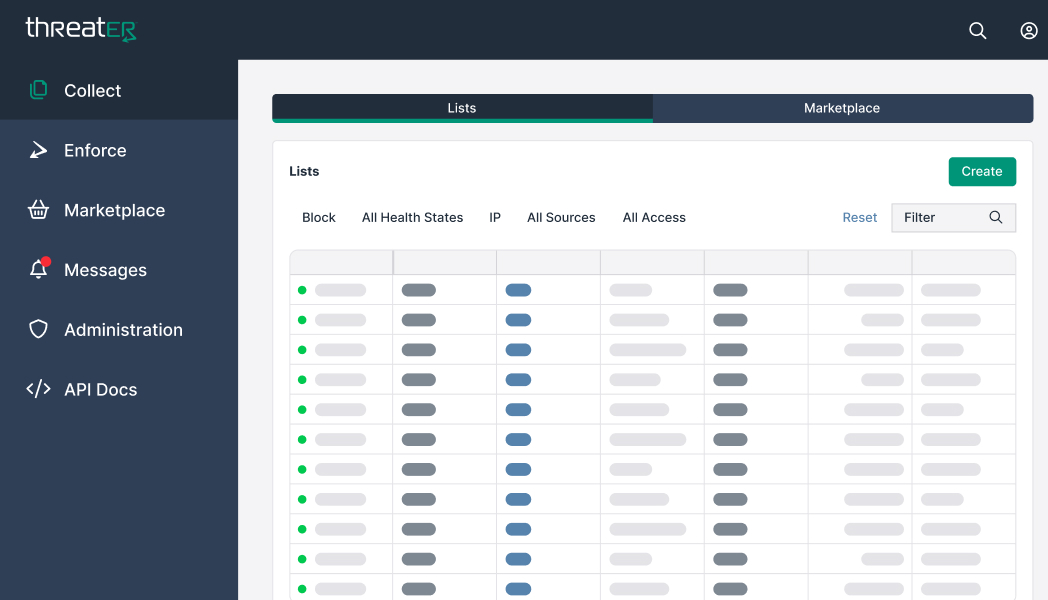
One free centralized SaaS solution to aggregate all of your threat intelligence
Why Collect?
Gain a better understanding of the risks facing your organization
Unique Cloud Attackers List
Access to best-in-class cyber intelligence feeds and threat lists
Access to Open Source Data
Compile and utilize up-to-the-minute intelligence for all your tools and technologies.
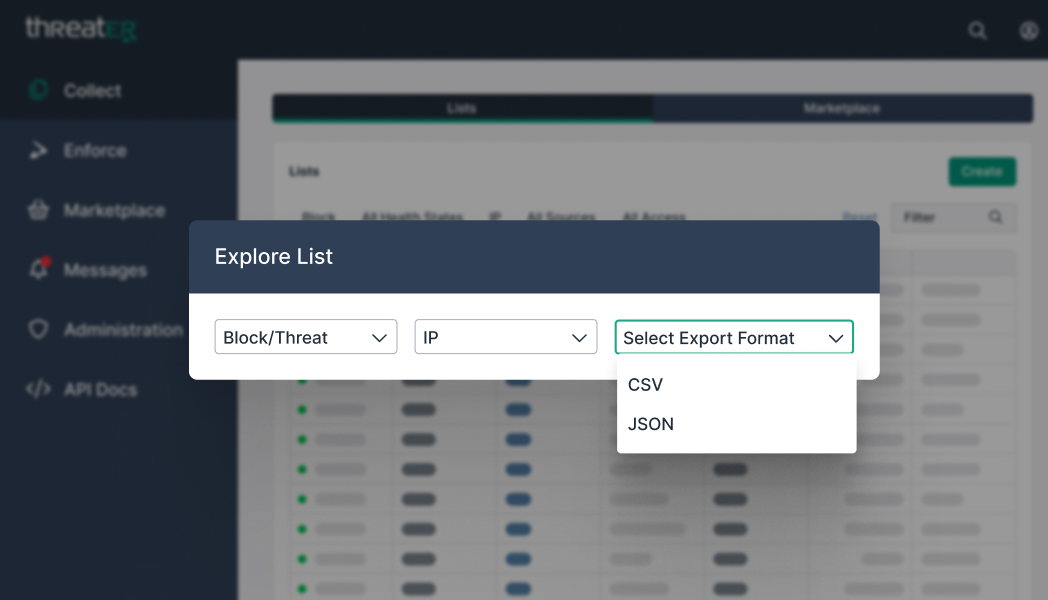
Export Lists to your Firewall
Feed your firewall the intelligence it needs
Additional Features
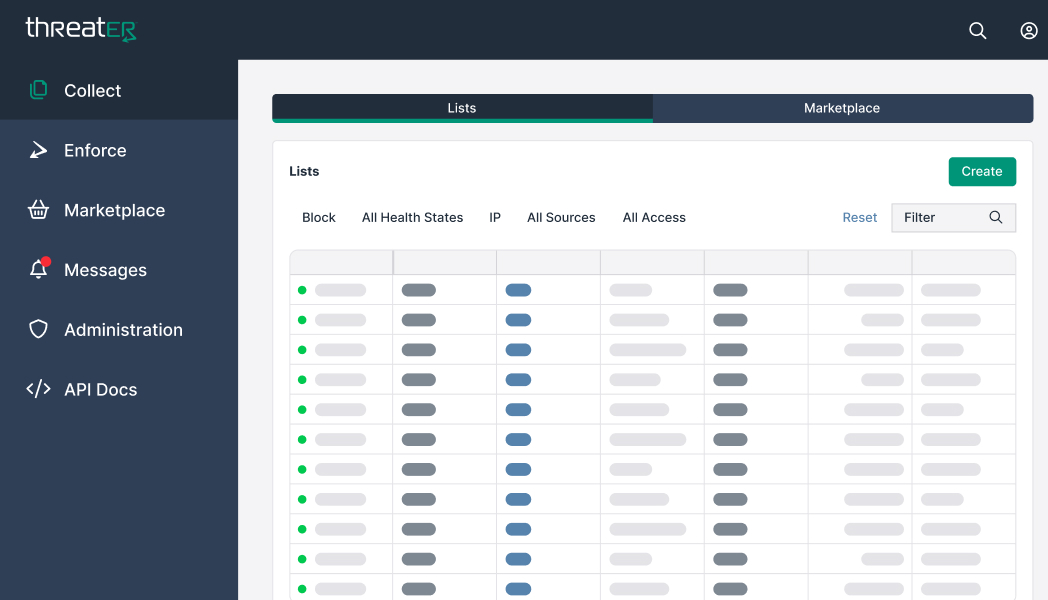
One central place to manage your cyber intelligence, including your own lists, feeds, and intelligence sources.
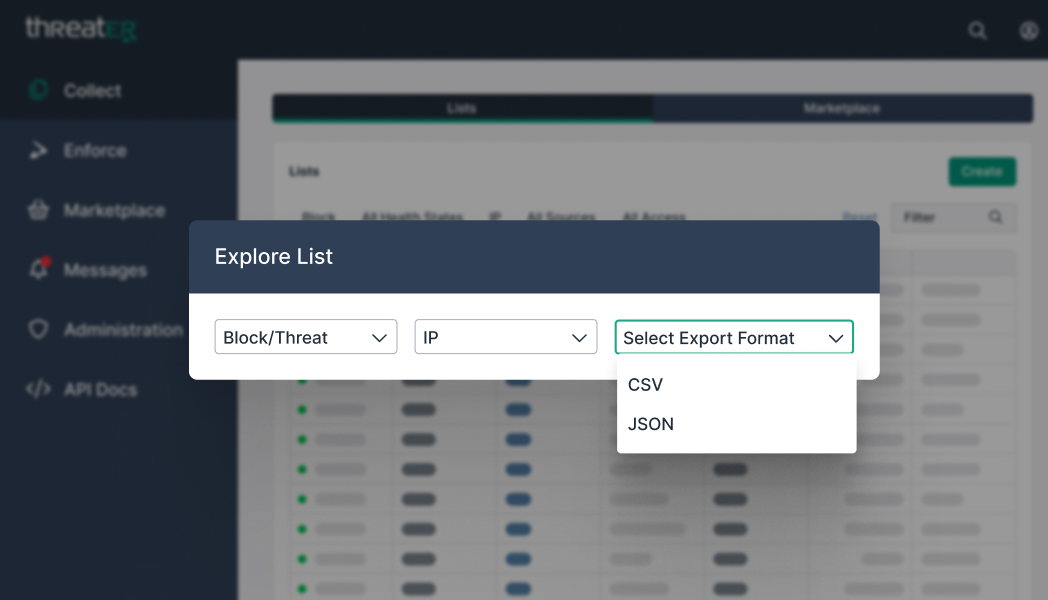
Leverage all your managed cyber intelligence by integrating your lists into other security tools and technologies.
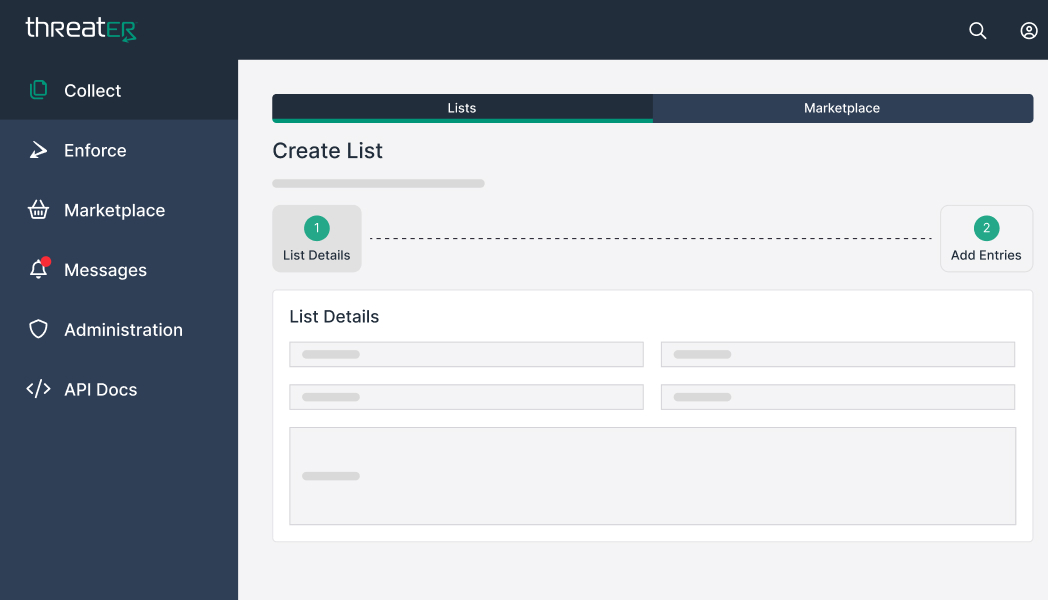
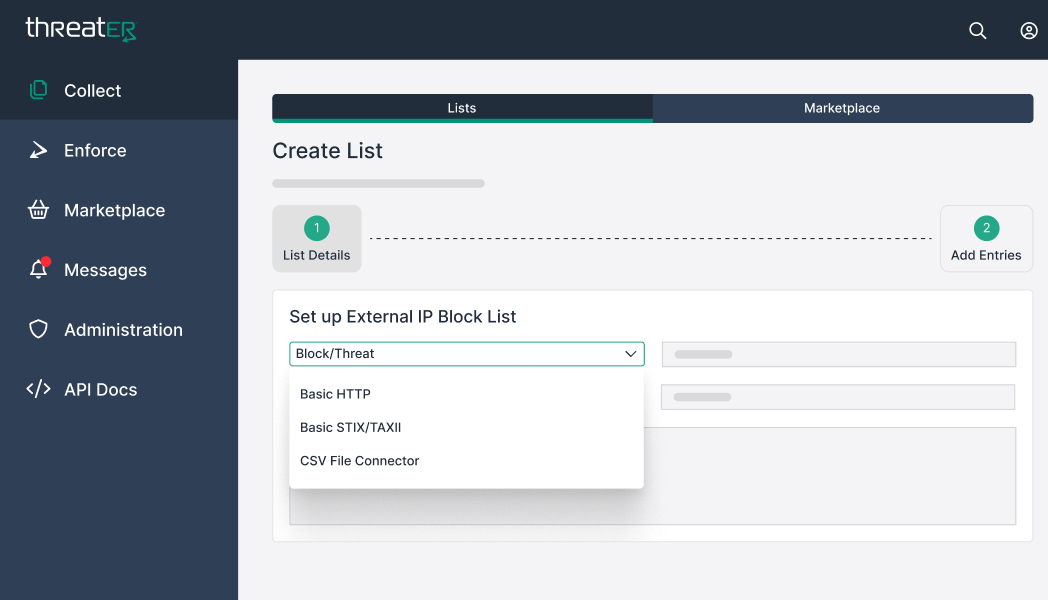
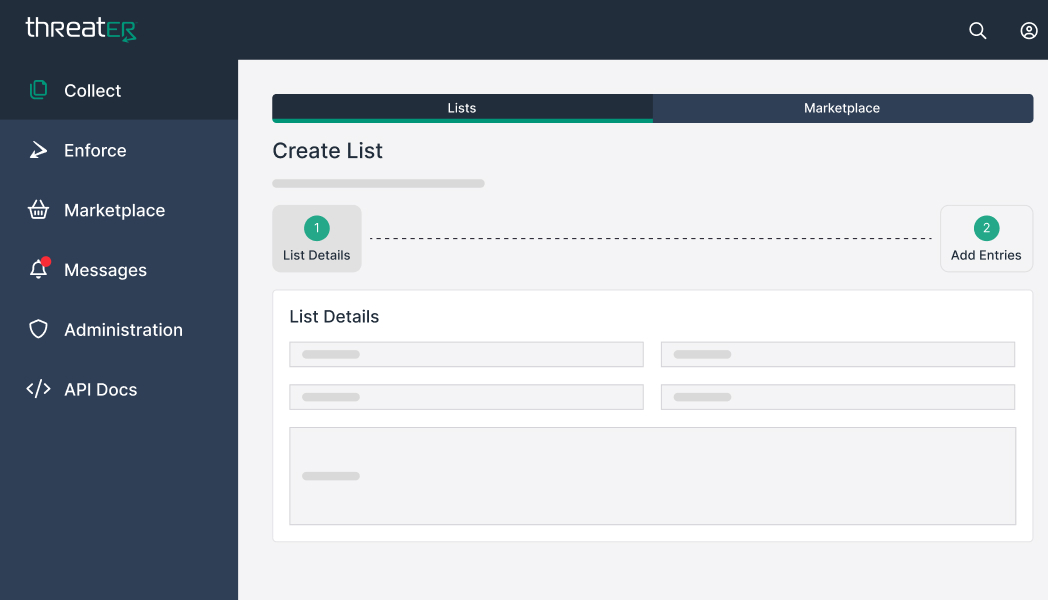
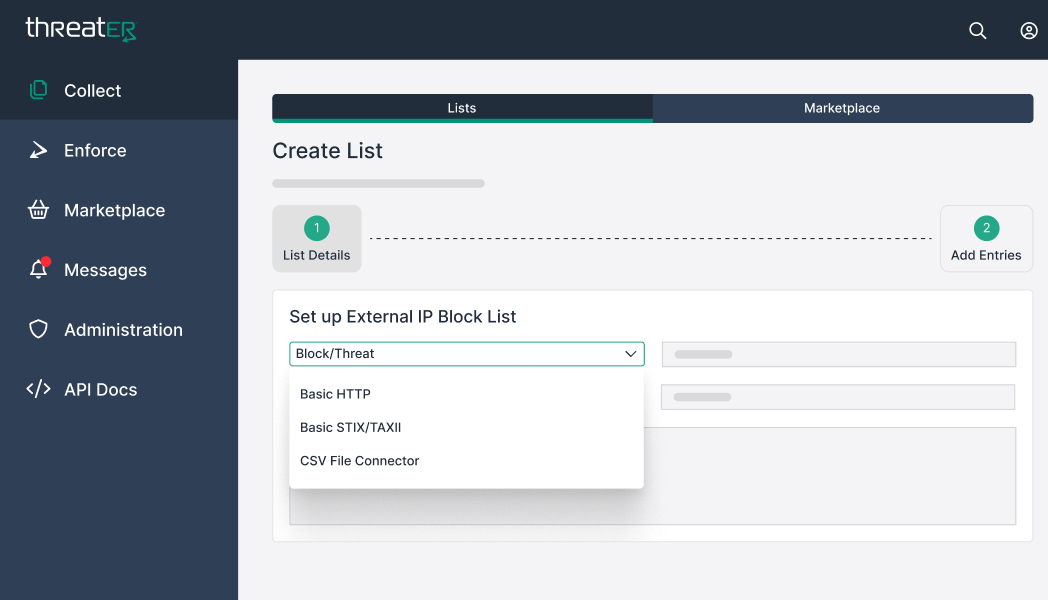
Easily create lists within the Collect platform to manage your organization’s cyber intelligence.
Integrate your tools and technologies into the Collect platform to give them an unparalleled, up-to-the-minute view of the threat landscape
Leverage best-in-class cyber intelligence to automatically block known threats at the line speed when you upgrade to Enforce.

One central place to manage your cyber intelligence, including your own lists, feeds, and intelligence sources.
Leverage all your managed cyber intelligence by integrating your lists into other security tools and technologies.
Easily create lists within the Collect platform to manage your organization’s cyber intelligence.
Integrate your tools and technologies into the Collect platform to give them an unparalleled, up-to-the-minute view of the threat landscape
Leverage best-in-class cyber intelligence to automatically block known threats at the line speed when you upgrade to Enforce.

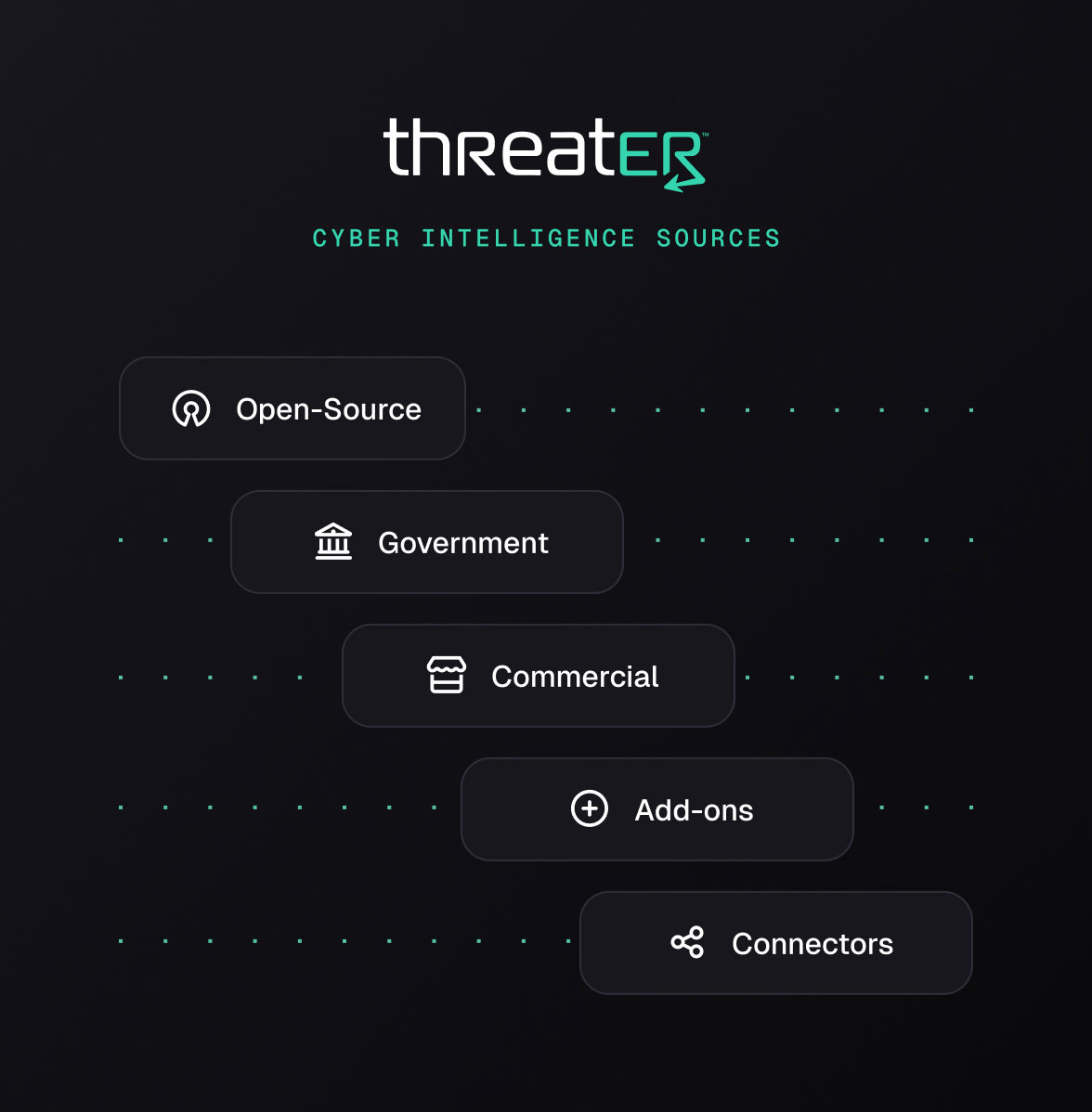
Don’t rely on one vendor’s view of the threat landscape for your cyber intelligence
- Source on near-unlimited cyber intelligence data by focusing on known threat actors
- Aggregate cyber intelligence from the entire community, including government agencies, open source organizations, and private companies dedicated to gathering, analyzing, and disseminating information about cyber threats, vulnerabilities, and activities.
Upgrade to Enforce
Block All Known Threats
Free Data Sources with Enforce Subscription
Millions of well-vetted malicious indicators of compromise (IOCs)
Millions of malicious domains and associated IP addresses
Known-good data (including Akamai, Amazon Cloudfront, Cisco Webex, Cloudflare, and more)
Utilize the threatER Marketplace
With one click, you can add cyber intelligence feeds and Enforce them in your network
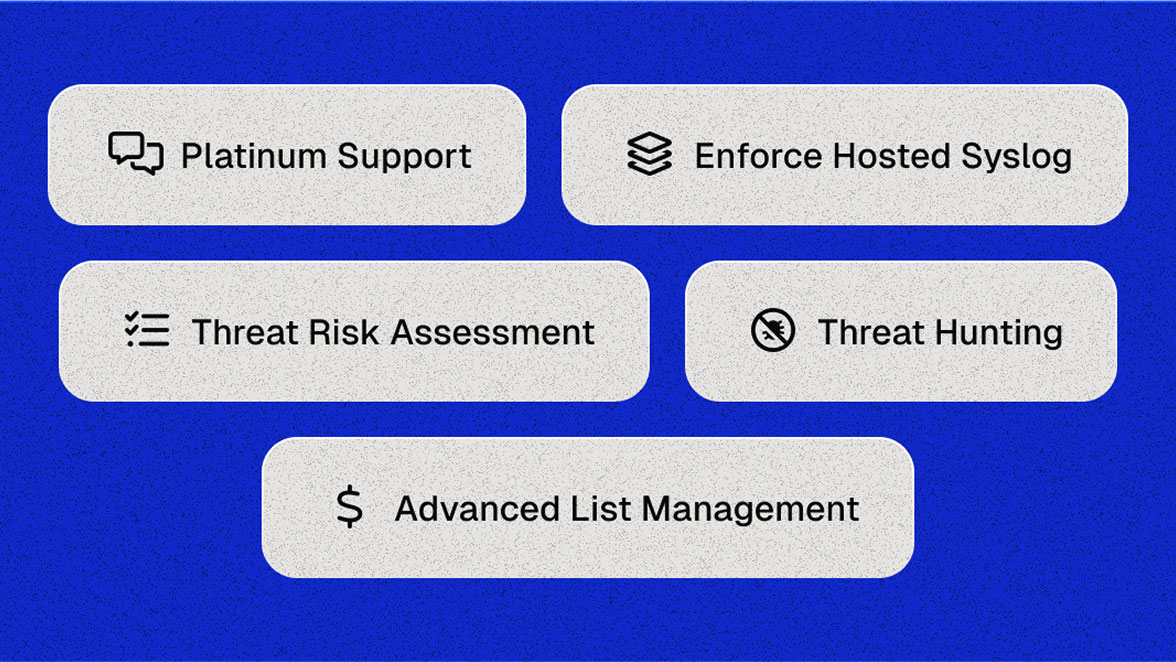
Cyber Services
Learn how threatER can help manage and resolve threats in your network.

Cyber Sources
Add more cyber intelligence feeds and lists to your intelligence platform, including industry-specific subscriptions.
Contact Us
Looking for more?
Think of something that should be added to our Collect subscription? Let us know here!