Splunk Enterprise Security Integration with Threater
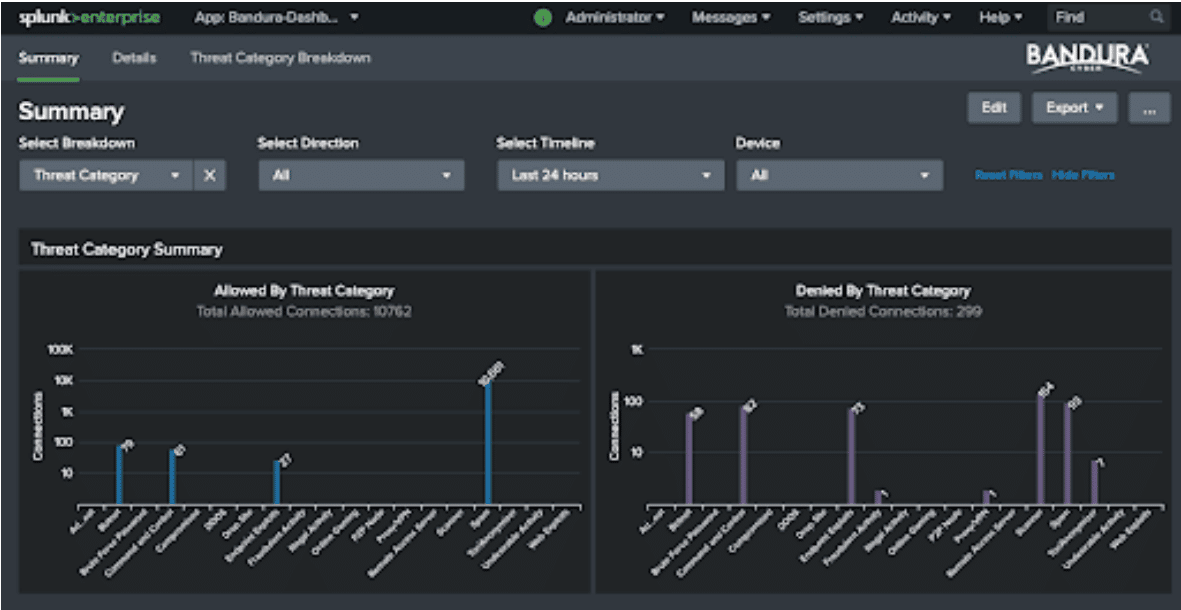
The integration of Threater and Splunk Enterprise Security combines security information and event management (SIEM) with network security powered by real-time threat intelligence.
Threater blocks known bad traffic at scale using a combination of simple, innovative technology and best-in-class threat intelligence. Splunk Enterprise Security is widely used by leading security organizations to detect, analyze, and respond to threats quickly. The combination of the two platforms provides improved protection from cyber threats and more effective and efficient threat detection, investigation, and response.
Benefits
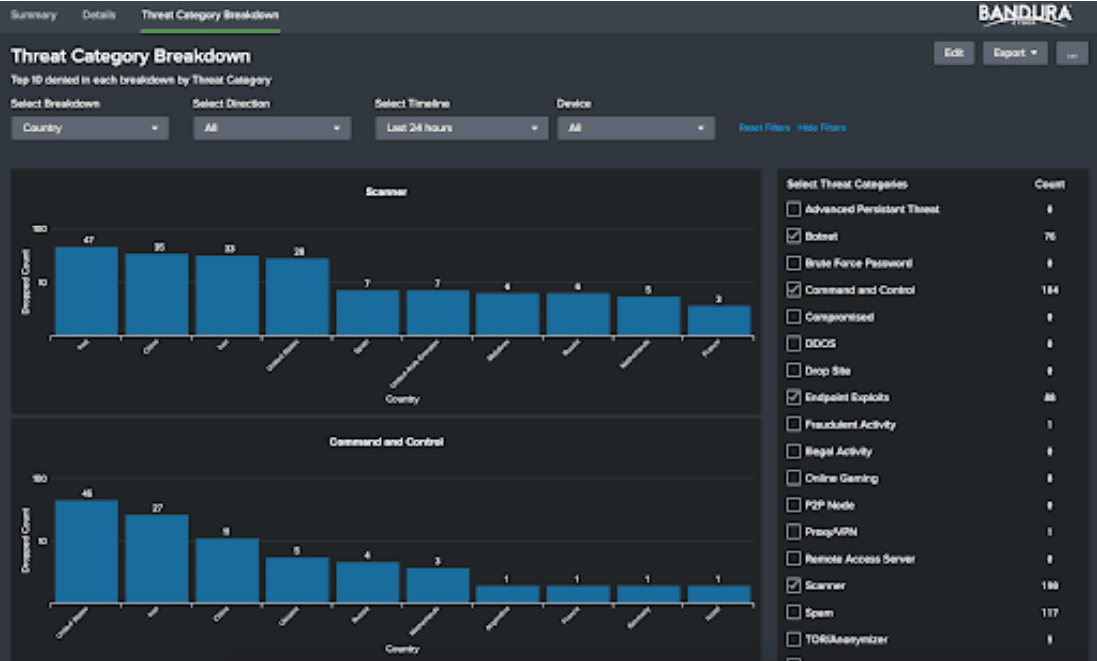
Comprehensive visibility into your security posture.
Improve threat detection.
Reduce the time to investigate and respond to security incidents.
Features
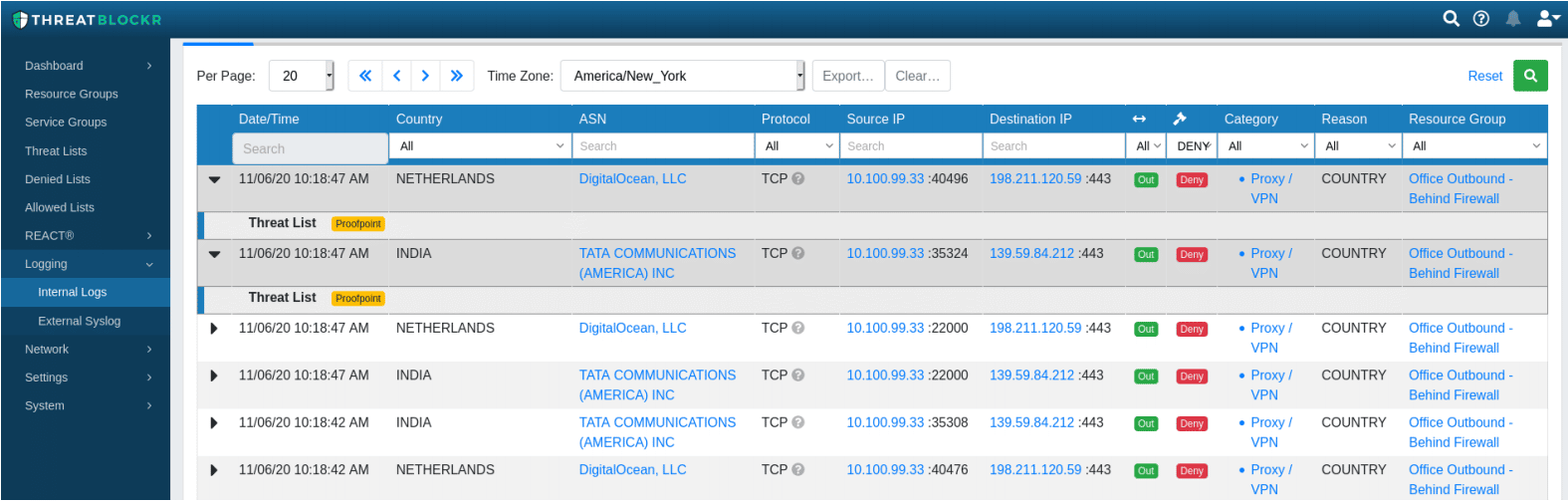
Leverage Splunk Enterprise Security for long-term storage of Threater logs.
Aggregate logs from multiple Threater appliances in Splunk
.
Use more customizable and advanced analytics, visualization, and reporting capabilities.
Correlate Threater logs with logs from other security controls and systems.