ThreatQuotient Integration with Threater
ThreatQuotient and Threater have joined forces to make threat intelligence more actionable, automated, and scalable.
Threater and ThreatQuotient have partnered to make threat intelligence more actionable in an effort to further fuel threat-centric security operations. This powerful integration enables organizations to strengthen network defense by proactively using threat intelligence from ThreatQ’s Threat Library and the Threater platform to block IP and domain-based threats before they hit your network.
The ability to take action on threat intelligence is critical to maximizing its value. However, organizations often face challenges integrating threat intelligence into traditional network security controls like firewalls. Most firewalls have limited capacity to integrate third-party threat intelligence indicators, and managing external blocklists in firewalls is complex and time consuming.
Benefits
Strengthen network defense by taking action with Anomali threat intelligence to prevent inbound and outbound connections to malicious IPs and domains.
Reduce staff workload by automating IP and domain block listing at scale.
Maximize threat intelligence ROI by making it actionable and increase the ROI and efficiency of existing nextgeneration firewall investments.
Features
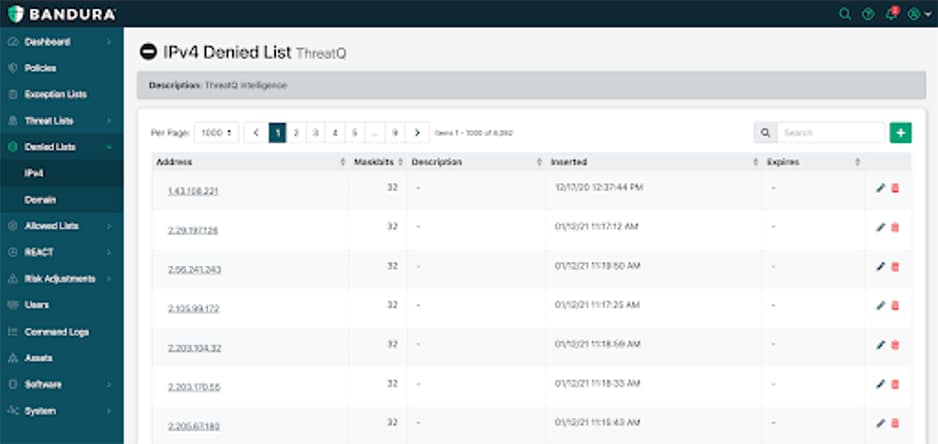
Threater integrates threat intelligence from ThreatQ and other sources to block up to 150 million known malicious IPs and domains before they hit your network.
ThreatQ automatically updates intelligence in the Threater platform, ensuring real time network protection and reduced manual workloads.
Threat intelligence-driven context from the network edge via the Threater platform enhances the value of ThreatQ threat intelligence with increased visibility into malicious IP and domain activity on your network.