ThreatSTOP Integration with Threater
ThreatSTOP and Threater have joined forces to make threat intelligence more actionable, automated, and scalable.
Threater and ThreatSTOP have partnered to make threat intelligence (TI) actionable at a scale that far exceeds what can be done with existing network security controls. This powerful integration enables organizations to strengthen network defense by proactively using TI from ThreatSTOP in the Threater platform to block IP and domain-based threats before they hit your network..
The ability to take action on TI at scale is critical to protecting networks from threats and maximizing the value of threat intelligence. However, many organizations experience significant challenges achieving this due to the significant limitations existing security controls have integrating TI. For example, most firewalls have limited capacity to integrate third-party TI indicators of compromise (IOCs). This forces organizations to operate with a limited subset of available TI resulting in suboptimal protection. It also leads to additional downstream effects including increased time and effort spent curating and managing external blocklists.
Benefits
Strengthen network defense Strengthen network defense by taking action at scale with TI to prevent inbound and outbound connections to malicious IPs and domains.
Reduce staff workload by automating IP and domain block listing at scale.
Maximize TI ROI by making it actionable. Increase the ROI and efficiency of existing next-generation firewall (NGFW) investments.
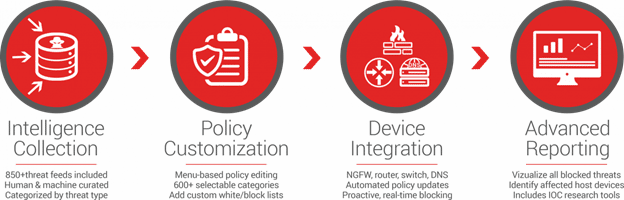
Features
Threater integrates TI from ThreatSTOP and other sources to block up to 150 million known malicious IPs and domains before they hit your network.
.
TI and policies from ThreatSTOP are automatically updated in the Threater platform, ensuring always current network protection and reduced manual workloads.
TI-driven context from the network edge via the Threater platform enhances the value of ThreatSTOP TI with increased visibility into malicious IP and domain activity on your network.