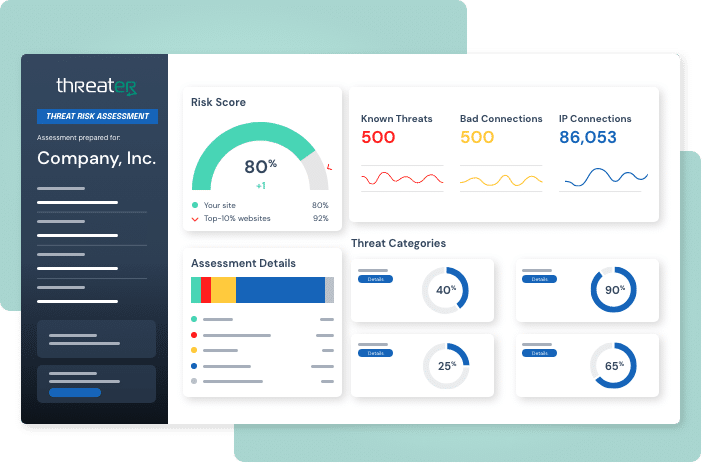
Run a Full Threat Scan in Minutes
Get a quick and comprehensive audit of your network security
In today’s threat landscape, it only takes one malicious connection coming into or leaving your network to cause a cyber attack.
Please complete the form with your Firewall information to receive a customized report. We will then follow up with directions on how to upload a log sample.