Cloud Network Protection Wherever You Need It
threatER protects your network, no matter where your network is.

threatER can run in all three major cloud providers: Azure, AWS, and Google Cloud.
Once deployed, threatER Enforce works exactly the same as if your network is on-premise, aggregating best-in-class cyber intelligence and blocking traffic to and from known threat actors at line speed.
By leveraging Gateway Load Balancers, threatER Enforce software interacts with the threatER portal in exactly the same way in the cloud as it does with on-premise deployments. That means no separate code bases based on deployment types, no update lags, with no exceptions.
As of March 2024, threatER is proud to support ARM as a new deployment addition, further allowing us to operate anywhere and everywhere.
AWS Graviton ARM processors are cost effective, high performance options for cloud customers, and threatER is now ready to deploy on them.
In the cloud, we understand that every cost is an operational cost. This means flexible deployment options for your security aren’t a luxury, they’re a necessity. threatER can deploy seamlessly on ARM processors, giving customers the flexibility to help save operational costs both now and exponentially in the future.
Simple Deployment, Immediate Protection
threatER Enforce deploys in the cloud in 15-30 minutes and can instantly start protecting your cloud network.
We provide vendor-specific deployment and installation templates to make sure your instance is up and running as quickly as you need.

More Intelligence Means More Protection
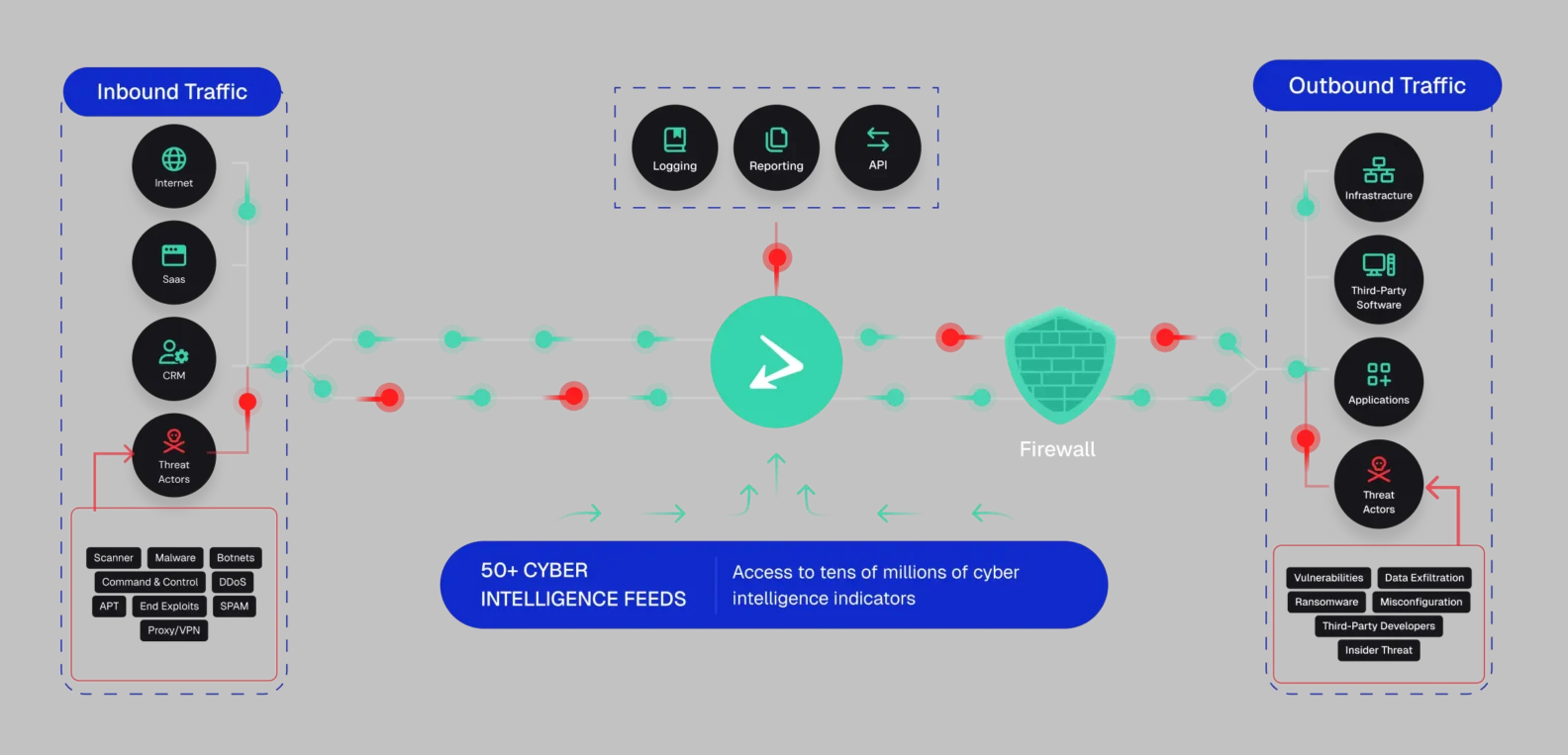
threatER Enforce doesn’t rely on just a few proprietary views of the cyber intelligence landscape. We aggregate 50+ best-in-class public, private, and open source cyber intelligence feeds, with the ability to add as many more as you can find, all updating automatically with up-to-the-minute intelligence. This gives your security stack the widest view of the threat landscape possible, allowing you to block more traffic to and from known threat actors.
All threatER subscriptions include our “Cloud Attackers” intelligence list, which includes ~15,000 indicators of known threat actors actively attacking the cloud. This list is curated by threat intelligence professionals at threatER, which means even more protection to your cloud network.

